Setting up Single Sign-On involves very detailed settings, and every provider and customer environment is different. If a user is inexperienced with SSO, getting all the identifying data and settings correct may take several attempts to allow for secure and reliable authentication. It is recommended to make sure someone with experience in SSO and IT infrastructure is available to streamline the process. Decisions support team is available to help but may not be able to answer questions or solve problems unique to a company.
Overview
Decisions allows users to use Single Sign-On for Multi-Tenant Environments using OpenId and SAML Module.
Prerequisites:
- A metadata URL
- Account created and assigned to Okta URL
- SAML Module installed. To learn more about installing modules, see Installing Modules in Decisions.
- A public-facing IP is needed for users to log in from a different VM.
Accounts created before the SAML module is installed will need to be updated before using Single Sign-On. Please contact support on how to update the account. Learn how to modify accounts after setting up SSO in the SSO Basics article.
Configuration
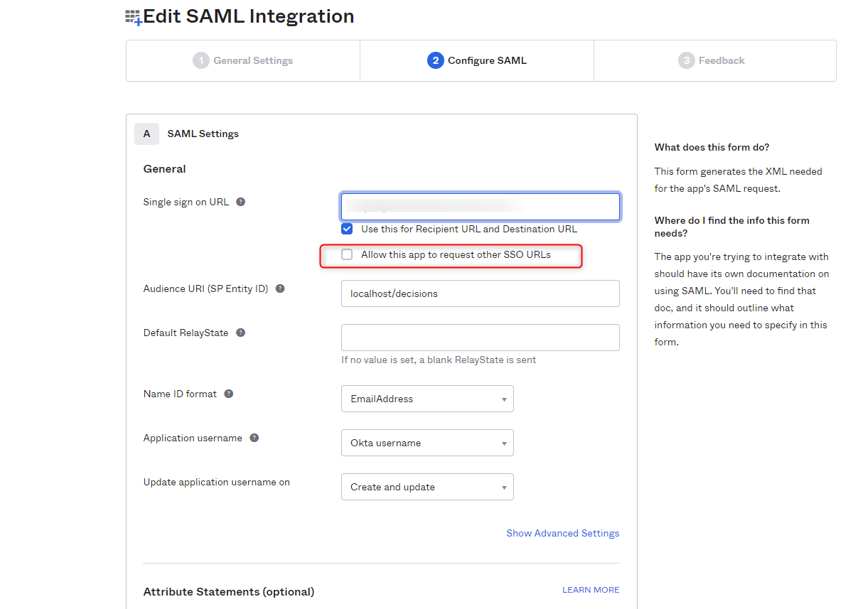
- In the OKTA SAML settings, ensure that the Single sign-on URL is configured as http://[Name of server]/[Name of Control Instance]/SAML/AssertionConsumer.
- Uncheck the option. Allow this app to request other SSO URLs.
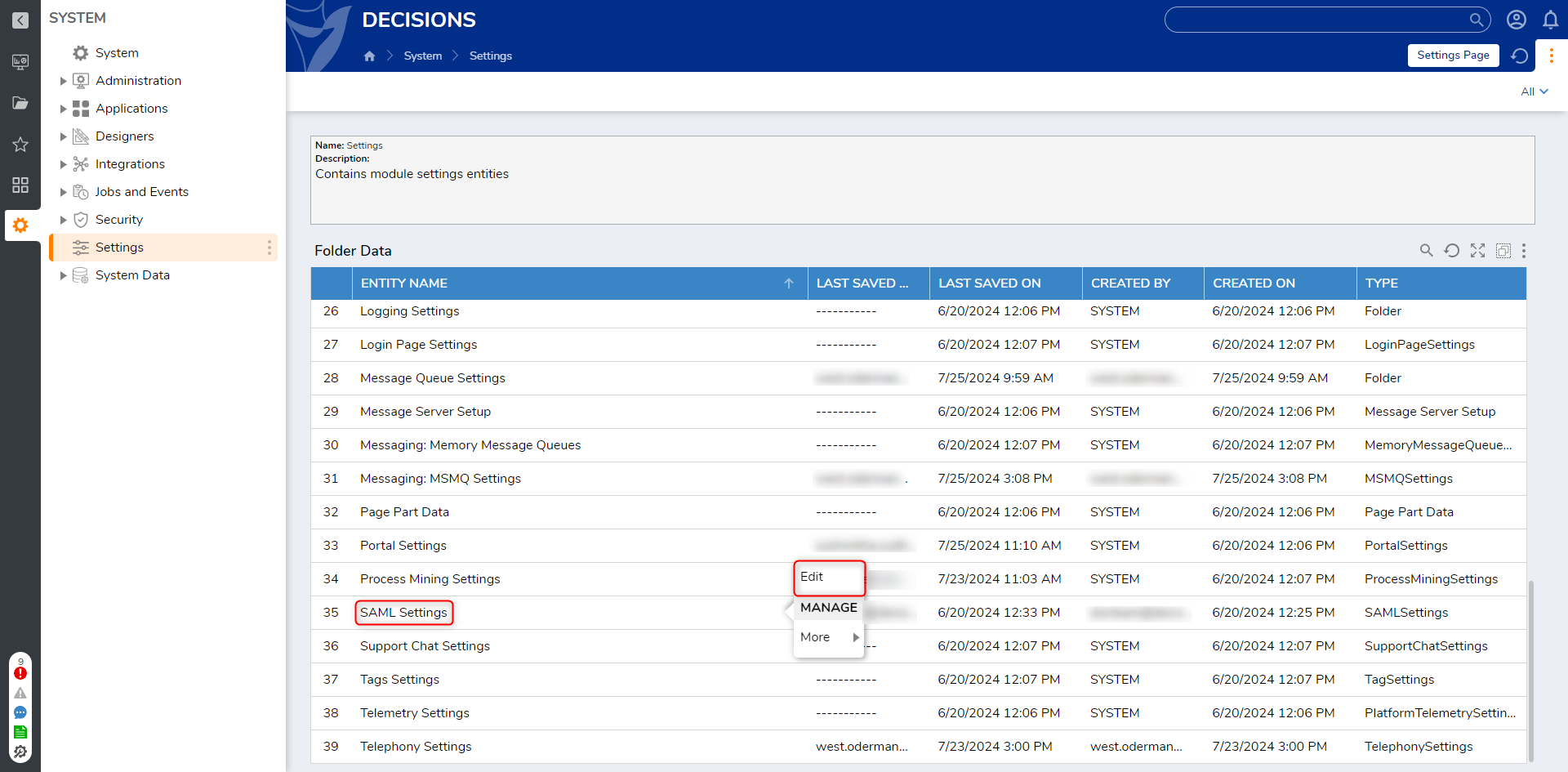
- In Decisions Studio, navigate to System > Settings, right-click SAML Settings, and select Edit.
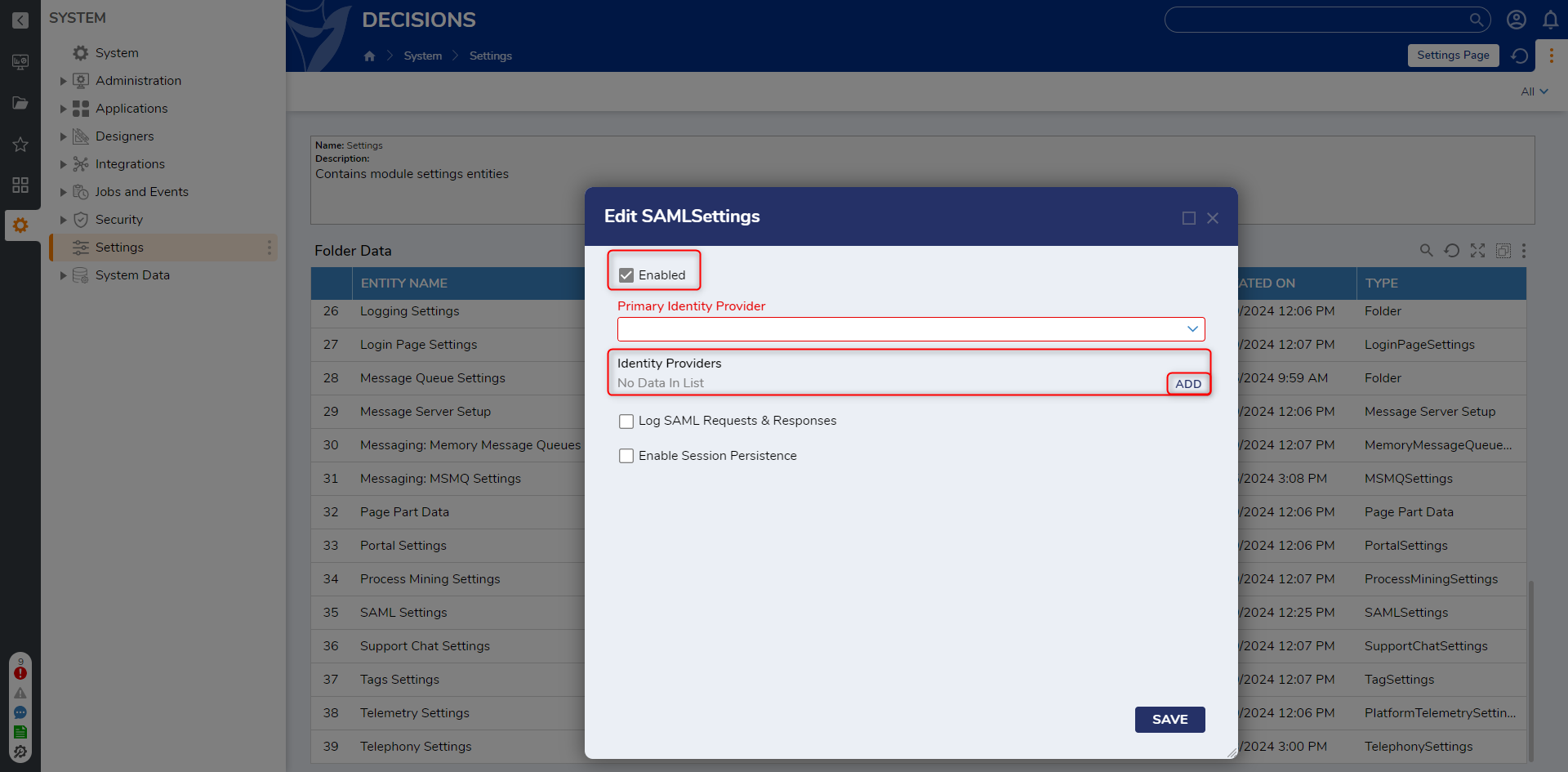
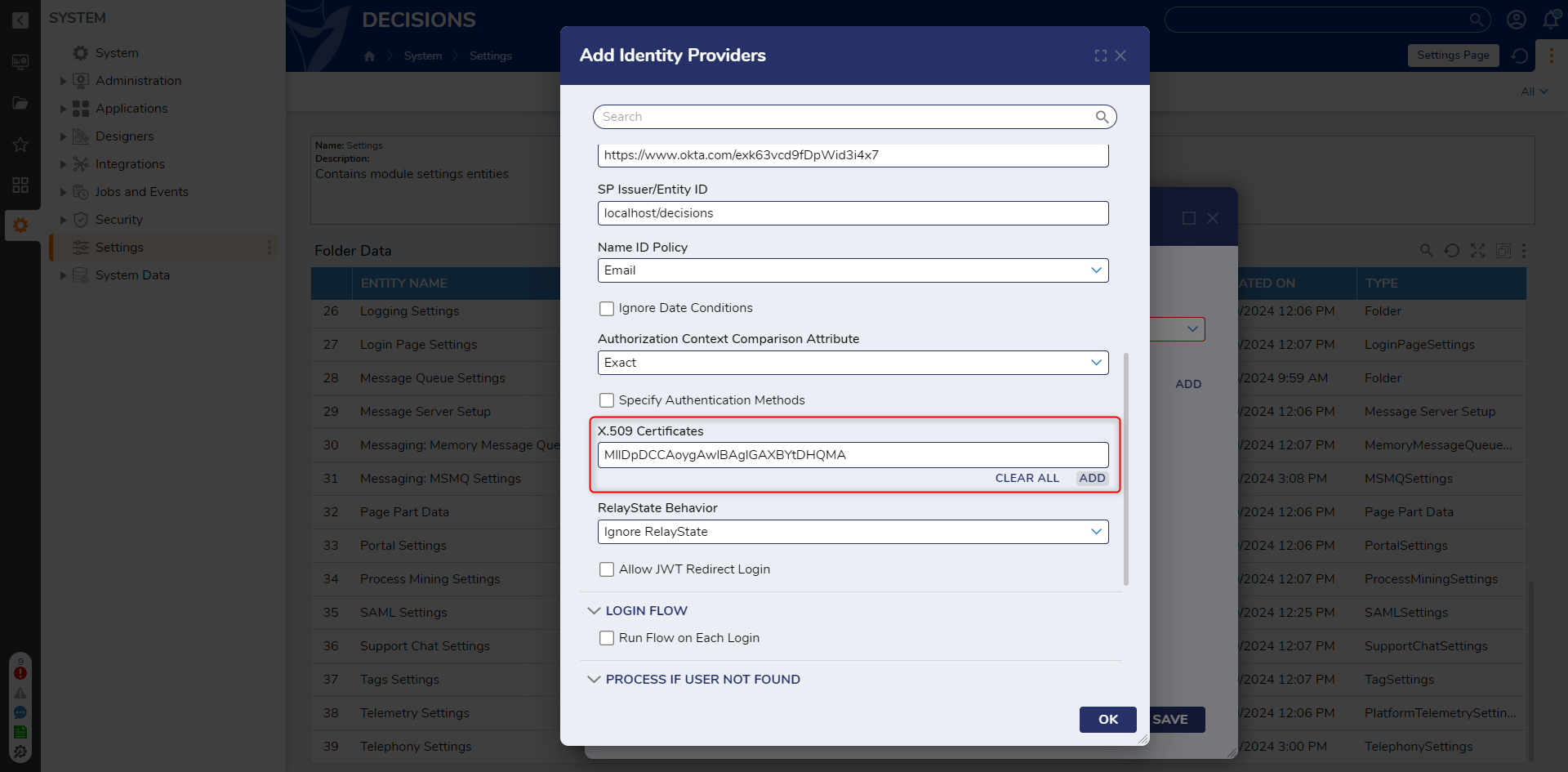
- From the Edit SAML Settings window, check the Enabled box. Then, under Identity Providers, click ADD.
- From Add Identity Providers, provide a Display Name. Under Metadata Document Preference, select Fetch Metadata From URL. Then, map the applicable Metadata via the chosen method. The Metadata URL is a required input. Providing it will automatically fill in all fields of the Module except for the SP Issuer ID, which is the Portal Base URL.
.png)
- Under the PROCESS IF USER NOT FOUND category, select Run Flow In Background. Under Run Flow, click PICK OR CREATE FLOW and pick SAMLDefaultCreateAccount.
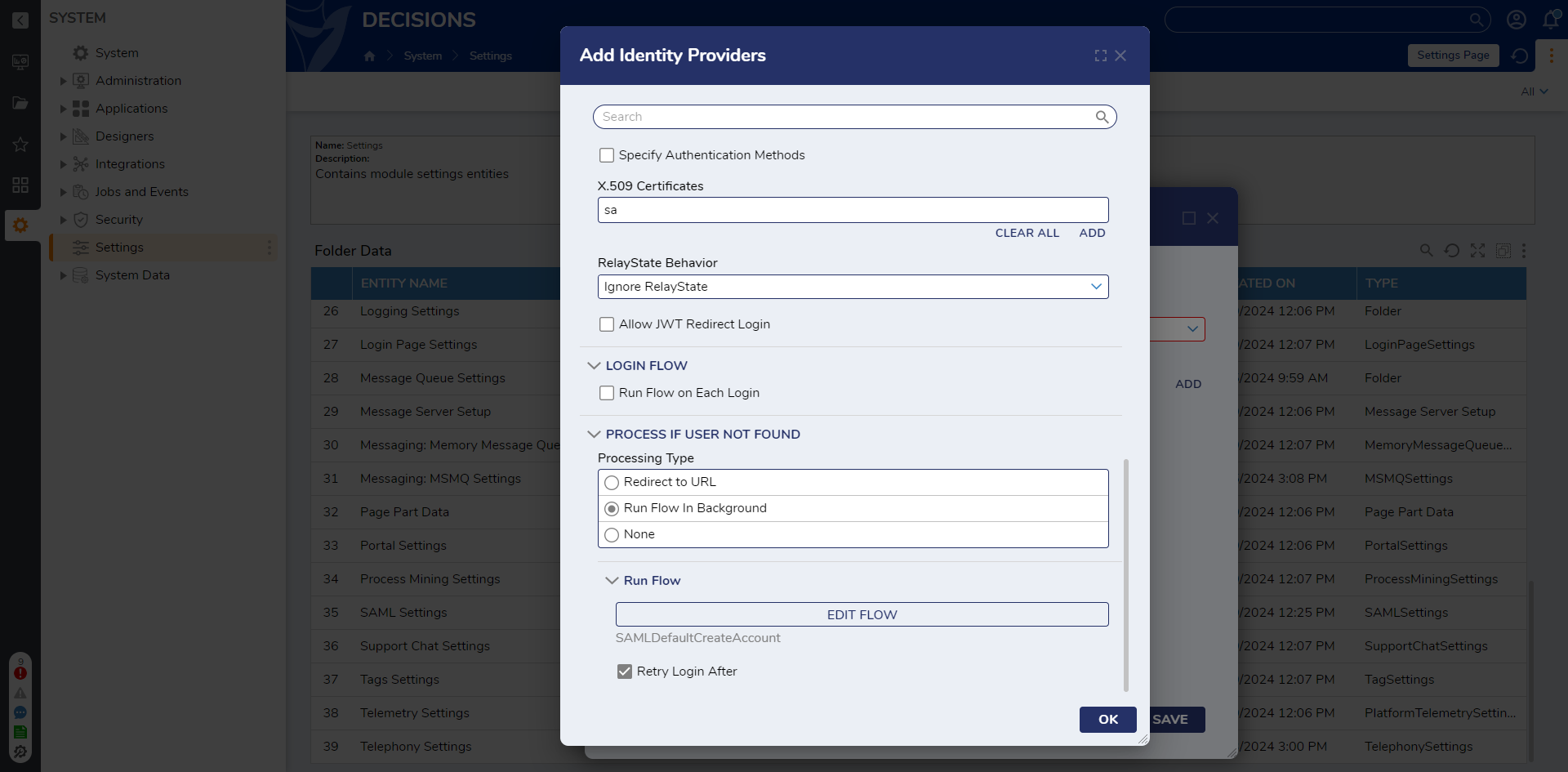
- If manually configuring the module, click ADD under X.509 Certificates, and add a valid x509 Certificate. Click OK. If the metadata URL were used, the X.509 certificate would automatically be pulled. For more information on x.509 Certificates, see What is an x509 Certificate?
- Click OK.
- In the Edit SAMLSettings window, select the newly added Identity Provider from the Primary Identity Provider list. Select the Log SAML Requests & Responses option and click SAVE. These requests and responses are kept in a set of logs called SAML found at C:\\Program Files\Decisions\Decisions Server\Logs.

Enabling SSO
Before enabling SAML SSO, configure at least one Admin user to work with SAML SSO or else there will be no admin users who can log into the system after enabling. When SSO is enabled, no local users can log in. If this is accidentally done, disable SSO and then log in with local users.
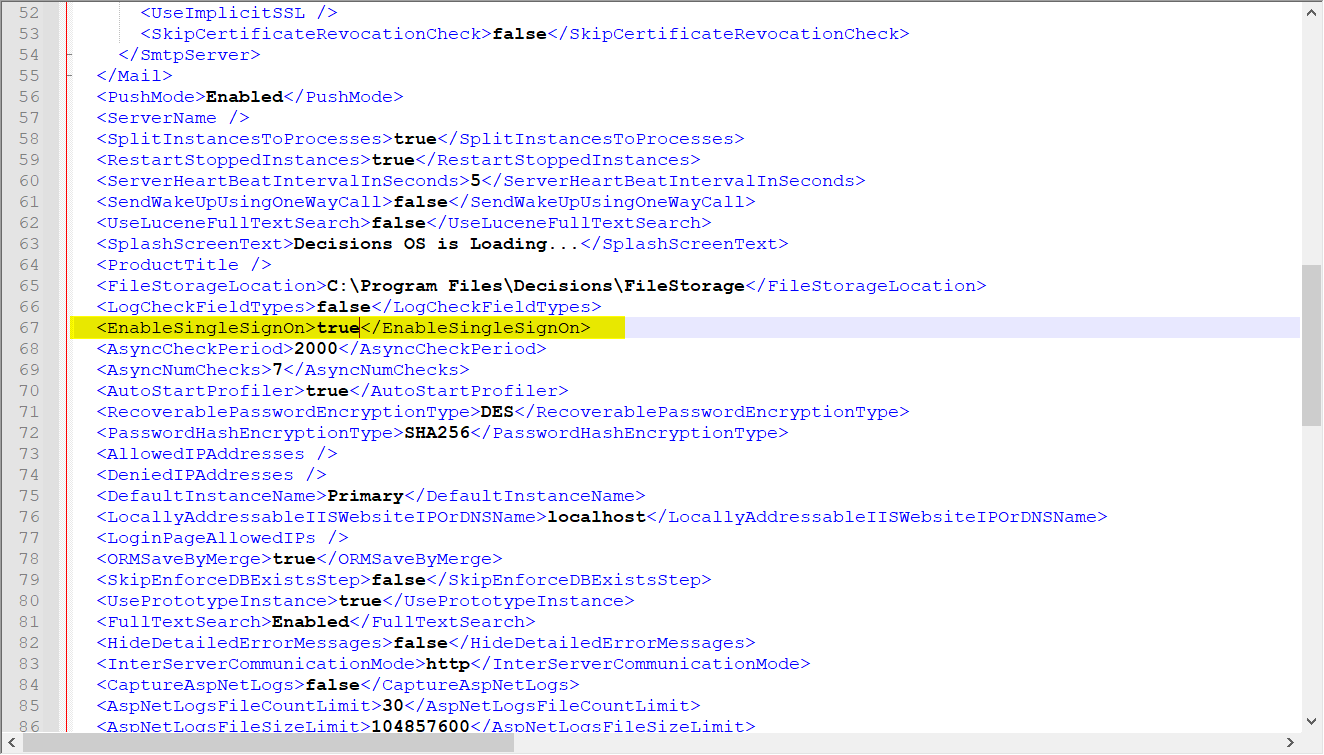
- Navigate to C:\Program Files\Decisions\Decisions Server and open the Settings.xml in a Text Editor.
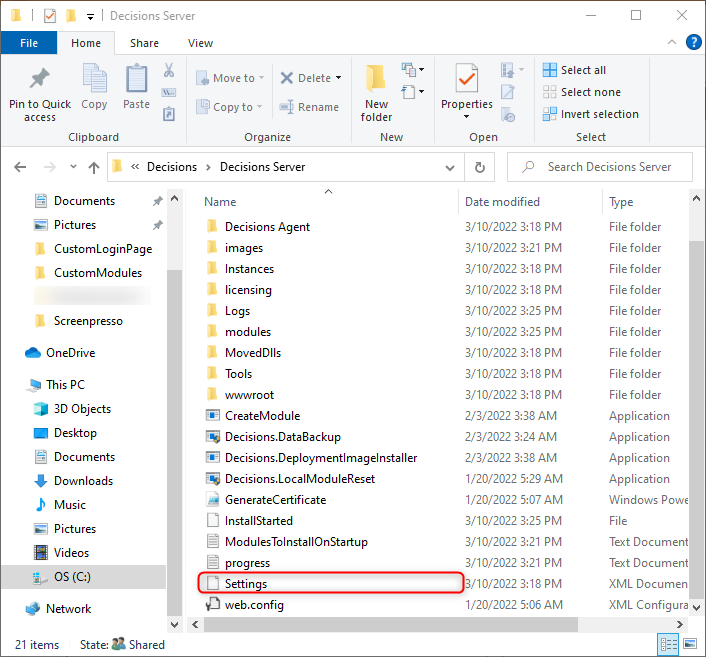
- Locate the <EnableSingleSignOn> line and change the false value to true. Save and close the file.
- Restart the Decisions Server.
- Continue testing on an Incognito Session; use the first open session to uncheck the Enabled button in the SAML module should something not work. This saves users from setting EnableSSO to false and restarting the Decisions Server again.
Troubleshooting
If a user wants to convert a local account to a SAML/SSO account or if a user receives errors when updating the User Identifier:
- Modify the UserID of the account
- Use SQL to modify the entity_account table and change the type of account
- Create a new account after SAML has been turned on and add it to the admin group
If the redirect is working only on a refresh of the initial login:
- Check the Retry on Log-In checkbox
- Ensure “/Login” is at the end of the Sign-On URL (case-sensitive)
When there is a "Context can only be used from localhost" error:
- Add the IP/Domain to <LoginAllowedIPs></LoginPageAllowedIPs> in the Settings.xml file
For further information on Active Directory, visit the Decisions Forum.